With the current outbreak of Coronavirus (2019-nCoV), officially named “Novel Coronavirus Pneumonia” or NCP by Chinese Health Authorities in China, businesses in the region have started to relook at their Business Continuity Plan (BCP) on how to effectively maintain business operation where physical contact between employees or individuals is being restricted to a high degree. Enterprise Singapore, supported by Singapore Business Federation has published a comprehensive Guide on Business Continuity Planning for 2019 Novel Coronavirus.
The gathering of a large group of employees in offices is now being avoided as much as possible, with companies instructing certain percentage of its employees to work away from the office or from home as much as possible to reduce the chance of infection risks in the office space.
In short, the standard business operations using the traditional mindset of mandating all staff to report to the office might now be a risky decision, in terms of risk of infection. However, this is highly dependent on the nature of business – such as operators for heavy machinery are still required to report to work, or telemarketers only requiring a laptop and internet to work. The reliance on digital communication channel is now critical as this is something that the current coronavirus cannot take advantage of. And NO, I’m talking about the actual infection and not cybercriminals taking this opportunity for email phishing or creating malware in the name this outbreak.
If you are one of many businesses that have not put in place a robust Business Continuity Plan (BCP) to mitigate current risks, now is the time to relook at your business operations, processes and infrastructure and do something about it. The authorities have mentioned that it could take months before this outbreak is over. They have also mentioned that the coronavirus is more infectious than Severe Acute Respiratory Syndrome (SARS) that was discovered and recognised in February 2003, however, Coronavirus fatality rate is lesser, according to the authorities.
Businesses should put the focus on considerations on the short-term situation where employees may be restricted to work outside of the office as much as possible. Businesses will need to rely on the current digital infrastructure, or even look into new solutions to support the sudden surge of digital communication requirements.
For companies with robust BCP in place, working remotely from home may not be a problem. In Netpluz, we allow our employees to apply for telecommuting, or work from home in case a need arises. Netpluz utilises the Microsoft O365 platform where our employees are able to conduct their day to day operations, such as conferencing, file-sharing or even work together on a single document. The platform enables our employees to maintain constant contact with each other via this platform. CRM & ERP platforms are accessible through Virtual Private Network (VPN). Sensitive data are being encrypted before being transmitted between employees’ laptop remotely and servers in Netpluz private cloud.
Video conferencing between employees, particularly the usual weekly meetings on business operations updates, shown no issues as Netpluz infrastructure is robust and highly available. Kudos to the engineering team and their experiences.
For customer-facing staff, such as the sales team, the inability to meet will not be the main factor that affects operations. The sales team may consider inviting their customers/prospects to meet through video conferencing with Microsoft Teams on Microsoft O365 platform.
For companies who are not well-prepared, such as not utilizing Microsoft O365 or similar platform and only relying on the traditional communication channel such as Whatsapp and traditional telephone, the predictable outcome would be employees not being able to work productively.
The following are some recommendations for businesses wanting to ensure business continuity:
- Consider categorising your employees in at least 2 teams (Team A & Team B), and avoiding physical interactions between the 2 teams.
Recommendation: Have at least a team to work remotely from home. Ensure that either team will be able to take on the role of the other team, should the need arises.
- Enabling your IT department/staff to deal with the sudden surge of connectivity issue, as more and more employees may be required to work from home.
Recommendation: Understand your bandwidth usage/utilization and upgrade to a higher bandwidth if necessary.
- File servers are hosted on-premise in the office location.
Recommendation: With the mobile workforce, a simple Virtual Private Network (VPN) connectivity is the basic requirement to access the file servers in the private network. Do contact us if you need VPN setup or even consultancy on your current infrastructure to support this feature.
- Ensure your employees are able to work from anywhere such as from home. Many SMEs, especially smaller companies have yet to collaborate digitally, as most may still prefer the in-person face to face meeting.
Recommendation: Consider working on Microsoft O365 and collaborate online with Microsoft Teams. Teams can be installed on multiple devices and employees can also work on their mobile phones on the go.
Netpluz is a Microsoft SPLA partner and Cloud Solution Provider.
- Ensure that all employees who work remotely do have the communication channel such as mobile phone to be contacted or to contact their customers or suppliers.
Recommendation: Ensure that employees desk phones are properly set up to ensure call forwarding. A solution such as MobileRoam ensures that employees are able to communicate with parties more productively. This service is recommended for employees that might be facing limited mobile plan subscribed. Businesses may also consider Cloud PBX and IP-Phones should the nature of the business requires high volume call traffics.
- Ensure that all employees’ endpoint such as laptops is installed with endpoint protection.
Recommendation: With employees working remotely and accessing the internet publicly, there will always be cyber risks of malware. To ensure that endpoints are properly secured with antivirus and anti-malware, Netpluz recommends Sophos Endpoint Protection such as Intercept X Advanced with EDR and MTR.
- All endpoints should have a proper backup solution in place.
Recommendation: As employees will move around to work remotely, there will always be a chance that the endpoint they work with will be stolen, lost or even data corruption. Having a proper endpoint backup solution such as Druva InSync ensures proper data protection and governance in this critical period.
- Working from home is not an option due to the nature of business, e.g. Financial or Sensitive Data Handling.
Recommendation: In such a scenario, businesses may consider splitting their team B onto a secondary work area, similar to business Work Area Recovery (WAR), which is also covered under a comprehensive BCP plan. Such secondary workspace or Work Area Recovery solutions include complete office facilities and equipment such as PCs, telephone systems, facsimile, photocopier, manager rooms, meeting rooms and general office areas to which our customers can quickly relocate key personnel to the recovery site and resume business as soon as possible. Contact Netpluz today to find out more, from cost-effective solution to a full-fledged WAR room.
- Businesses to relook at existing or even consider building a Business Continuity Plan (BCP).
Recommendation: As IT landscapes are getting more complex with the subscription of multiple SaaS solutions or even on-prem solutions, devising a comprehensive and robust business continuity plan may require the guidance or advisory from a managed communication service provider who has decades of experiences. Netpluz has been offering advisories in terms of BCP on IT infrastructure.
The above recommendations are some simple guidelines to enable your employees to continue to work remotely if required while waiting for the coronavirus outbreak to subside.
Solutions such as collaboration platform Microsoft Teams on O365 creates the modern workspace, where employees can collaborate without the need to be physically in a specific office. Companies that have proper BCP in place would have a competitive advantage in this crisis period.
For businesses who finally understands the importance of digital communication platforms and in need of assistance, Netpluz can advise, propose, implement and manage an end-to-end robust solution. Please contact contact@netpluz.asia to set up an appointment to discuss how Netpluz can support you in communication services.
Author: Rueburn Liang
Cyber Security is the protection of not only internet-connected systems (including hardware, software or electronic data) from theft or damage by cybercriminals but also from disruption of services following a successful cyber-attack.[1] According to the Cyber Security Agency of Singapore, 378 business email impersonation scams were recorded in 2018. This led to businesses in Singapore suffering close to S$58 million in losses. [2] Cybersecurity Ventures has reported that businesses will lose approximately $6 trillion to cyber-crime by 2021. [3]
One of the key challenges faced by organisations today is implementing cybersecurity measures to protect their internet-connected systems from the continuously evolving nature of cyber-attacks. And according to Code 42, 78% of security professionals believe that the biggest threat to cybersecurity is the negligence of employees. [4]
Cybercriminals exploit the weakest links in an organization’s IT security fabric. Often, the weakest link in any organisation is the employees. And yet a study of over 5,000 businesses around the globe by Kaspersky Lab and B2B International found that just over half of businesses (52%) believed that their cybersecurity would be at risk because of their employees. [5]

Common Cybersecurity Mistakes Made By Employees
In this section, we’ll be looking at the four principal errors made by employees that could expose organisations to cyber-attacks
1. Weak and Vulnerable Passwords
According to security experts, poor password management contributes to 81% of the data breaches.[6] With employees utilising the same password for multiple accounts, not changing passwords on a regular basis and using weak passwords (some examples as shown in the table below) put organisations at risk. [7]
Examples of weak passwords:
|
Password |
Type |
|
kathy5 |
Name-based |
|
Qwerty |
Keyboard sequence |
|
AbcAbc |
Repeating sequence |
|
dr1v3way |
Word-based with common letter and number substitution |
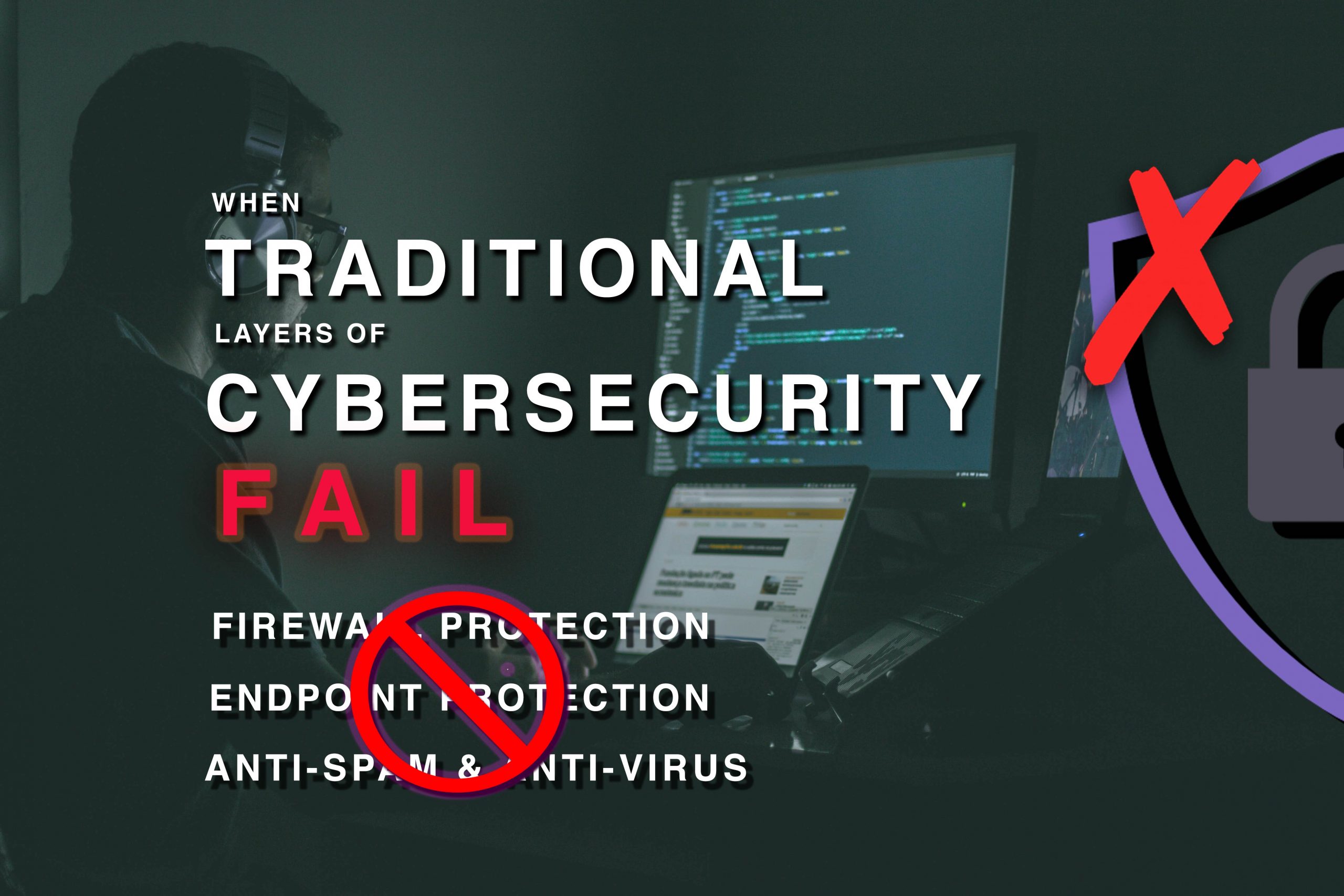
- Weak or Outdated Security Software
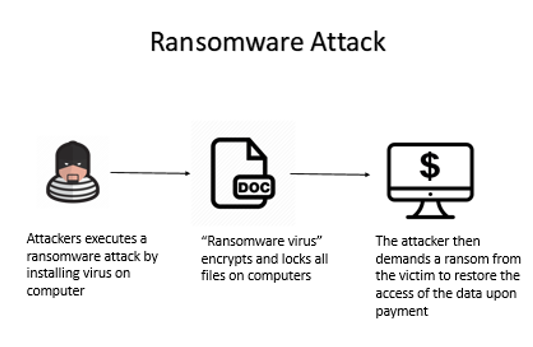
Keeping security software, web browsers and operating systems updated with the latest protection will deter cybercriminals from leveraging system vulnerabilities. However, many organizations do not keep up with the updates or fail to understand the consequences of not doing so. The consequences of an employee’s negligence could lead to a ransomware outbreak where the virus encrypts and locks all the files on the computer. The attacker then demands a ransom from the victim to restore the access of the data upon payment. [7]
Here is a diagram to illustrate how a Ransomware Attack is executed:
- Lax Email Practices
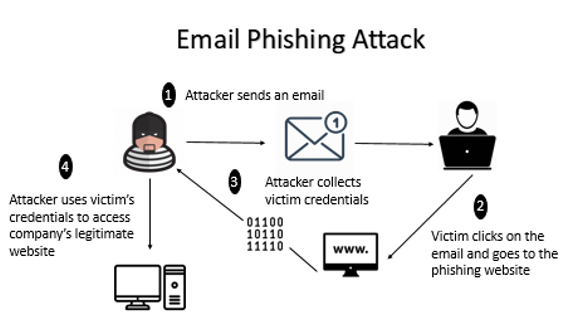
Despite repeated warnings against responding to unsolicited emails or text messages, employees continue to be targets of cyber-attacks such as phishing, social engineering, and smishing. These attacks occur when an attacker sends an email link to the victim. Upon clicking on the link, the victim will be directed to the phishing website where the attacker is able to collect the credentials of the victim. The attacker then uses the victim’s credentials to access the legitimate company’s website. [7]
Here is a diagram to illustrate how Email Phishing Attack is executed:
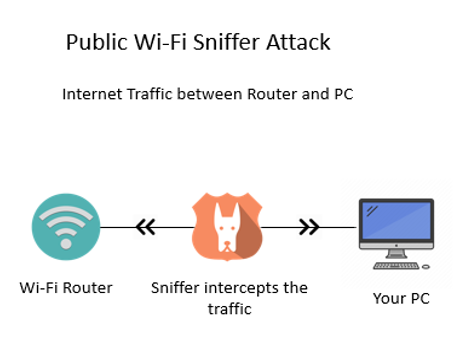
- Using Unsecured Networks
Utilising company devices on unknown networks increases the risk of cyber-attacks since data may not be encrypted over these networks and could easily be intercepted and subsequently stolen. For example, login details information can be revealed when there is an attempt to access emails on a public network. [7]
Here is a diagram to illustrate how a Public Wi-Fi Sniffer Attack is executed:
How can your company reduce these vulnerabilities?
In recent years, cyber-attacks have become more sophisticated and persistent due to weak security regulations enforced by companies. By now, you might be wondering how you could protect your data better. Sophos Intercept X Advanced with EDR and Druva inSync offer some possibilities that could help companies overcome poor practices done by their employees. These two products address the business challenges faced by organisations such as data protection, secure file sync and sharing, etc.
What is Sophos Intercept X Advanced with EDR?
Sophos Intercept X Advanced with Endpoint Detection and Response (EDR) is designed to stop the widest range of attacks. It can detect malware, provide exploit protection, defend against ransomware and more through a combination of modern and leading-edge foundation techniques. In an event of malicious activity, EDR provides users with a complete solution by providing them with a detailed report of the attack. This helps businesses understand the root cause of the attack and help them to avoid future cyber-attacks. [8]
Benefits of Implementing Sophos Intercept X Advanced with EDR
1) Deep Learning Malware Detection
Intercept X’s artificial intelligence is a deep learning neural network, an advanced form of machine learning that detects known and unknown malware without relying on signatures. Powered by deep learning detection, Intercept X has the best malware detection platform in the industry. This allows Intercept X to detect malware that slips by other endpoint security tools. [8]

2) Secured Data & Files
Intercept X utilises CryptoGuard technology to combat cyber security attack such as ransomware and boot-record attacks, making it the most sophisticated anti-ransomware technology available. Even if trustworthy files or processes are manipulated or stolen, CryptoGuard is able to interrupt and revert them to their original state. [8]
3) Detailed Report Analysis
With EDR, most threats are stopped before they can cause damage. Intercept X Advanced with EDR provides additional cybersecurity assurance with the ability to detect, investigate and respond to potential security threats. Thus, when a potentially suspicious file is detected the administrators are provided with an analysis of what the malware did and how it was executed. This helps your companies to understand the threats better and prevent them. [8]
Here is a quick overview of how Sophos Intercept X Advanced with EDR works:
What is Druva inSync?
Druva inSync provides a comprehensive solution for enterprise-grade data protection and management. It allows users to view their data sources and usage activities to ensure compliance. Administrators are also updated of any potential data risks that have been detected. Data collected are stored in a central repository, giving end-users seamless and constant access to the information. [9]
Benefits of Implementing Druva inSync
1) Centralised Data
Druva inSync allows collection of data through multiple devices like mobile phones and cloud-based applications. The collected data will be then stored and indexed in a central repository which makes it easier for an IT department to implement company policies. [9]
2) Real-Time Data Monitoring
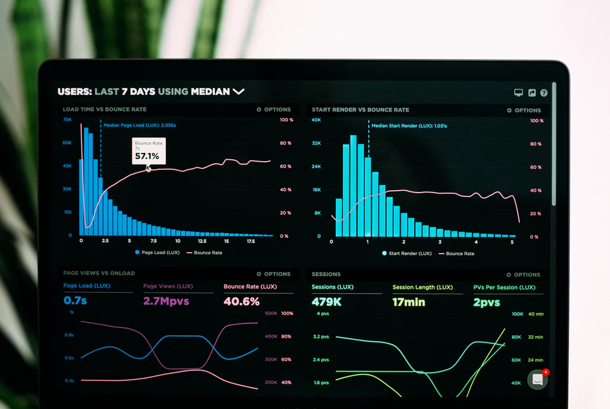
Druva inSync is equipped with an administrative dashboard where users can monitor their data activities and data usage in real-time. This allows administrators to easily discover compliance issues and resolve them quickly before they grow into larger problems. Real-time data monitoring also keeps your organisations safe. [9]

3) Ease of Compliance Enforcement
Druva inSync helps you save time when it comes to administering policies and regulations. This system comes with pre-configured compliance templates like PCI, GLBA and HIPPA. It also enables users to customise and create their own templates. Whichever template one chooses, one can be ensured that the app automatically search for any data risks. [9]

What other solutions can you integrate along with Sophos?
Cyber-attacks are carried out mostly through emails and unsecured networks. This could be resolved by integrating the following products with Sophos Intercept X Advanced with EDR. [10]
|
Solutions: |
Features: |
|
Intercept X and Sophos Email |
✔ Validates if malware has been installed on devices with compromised mailboxes |
|
Intercept X and Sophos Wireless |
✔ Blocks worm-like lateral movement, automatically isolating infected machines ✔ Prevents non-compliant devices from connecting to corporate data |
Summary- Sophos Intercept X Advanced with EDR and Durva Insync
There are many comprehensive cyber security products available in the market to mitigate cyber-attacks. Needless to say, the product chosen to safeguard the data plays a major role in preventing cyber-attacks against your companies.
Here is a quick summary of the benefits of Sophos Intercept X Advanced with EDR and Durva InSync:
|
|
Sophos Intercept X Advanced with EDR |
Durva inSync
|
|
Deep Learning Malware Detection |
✔ |
|
|
Secured Data Files |
✔ |
|
|
Detailed Report Analysis |
✔ |
✔ |
|
Centralised Data |
|
✔ |
|
Ease of Compliance Enforcement |
|
✔ |
|
Software Supported |
Windows 7 and above, 32 and 64 bits |
● Microsoft Office ● G Suite ● Box ● Salesforce |
The following are the factors that are needed to be taken into consideration when choosing between these 2 products. The key difference between these two products is that Sophos Intercept X Advanced with EDR protects internal data stored in the physical hardware whereas Druva inSync supports data stored on the cloud premises.
If you wish to find out more information on Sophos Intercept X Advanced with EDR or Durva inSync, you can visit us at Netpluz. Alternatively, you may book an appointment here for a free consultation.
Author: Jeyani D/O Ravichandran
References:
- “What Is Cybersecurity?” Cisco, Cisco, 10 Dec. 2019, https://www.cisco.com/c/en/us/products/security/what-is-cybersecurity.html.
- Tay, Rachel. “Businesses in Singapore Lost Nearly S$58 Million to Email Impersonation Scams Last Year: CSA Report.” Business Insider Singapore, 19 June 2019, https://www.businessinsider.sg/businesses-in-singapore-lost-nearly-s58-million-to-cyber-attacks-last-year-csa-report/.
- Cybercrimemag. “Cybercrime Damages $6 Trillion by 2021.” Cybercrime Magazine, 9 Dec. 2018, https://cybersecurityventures.com/hackerpocalypse-cybercrime-report-2016/.
- Kratikal Tech Pvt Ltd. “Humans Are the Weakest Link in the Information Security Chain.” Medium, Medium, 6 Mar. 2018, https://medium.com/@kratikal/humans-are-the-weakest-links-in-cyber-security-of-any-organisation-ac04c6e6e71.
- “The Human Factor in IT Security: How Employees Are Making Businesses Vulnerable from Within: Kaspersky Official Blog.” Daily English Global Blogkasperskycom, https://www.kaspersky.com/blog/the-human-factor-in-it-security/.
- “81% Of Company Data Breaches Due to Poor Passwords.” TraceSecurity, 10 Dec. 2019, https://www.tracesecurity.com/blog/articles/81-of-company-data-breaches-due-to-poor-passwords.
- Mical, Jason, et al. “11 Ways Employees Can Be Your Weak Link for Cybersecurity.” Security Boulevard, 9 Sept. 2019, https://securityboulevard.com/2019/09/11-ways-employees-can-be-your-weak-link-for-cybersecurity/.
- SOPHOS Intercept X, SOPHOS, https://www.sophos.com/en-us/medialibrary/PDFs/factsheets/sophos-intercept-x-dsna.pdf.
- “Druva InSync Review: Pricing, Pros, Cons & Features.” com, 12 Aug. 2019, http://comparecamp.com/druva-insync-review-pricing-pros-cons-features/.
- “Synchronized Security.” Synchronized Firewall & Endpoint Protection with Sophos, https://www.sophos.com/en-us/lp/synchronized-security.aspx.
Importance of cybersecurity for cyber-attacks
Why do we have fire drills when we hardly or never encounter fire? The same goes for cybersecurity – we do not know when we will encounter a cyber-attack. Cybersecurity is the practice of protecting systems, networks and programs from digital attacks. Successful cybersecurity has multiple layers of protection spread across computers, networks, programs or data that one intends to keep safe. 1
Impact of cyber-attacks on companies
Cyber-attacks can cause financial loss for the business as well as reputational damage. When there is a loss in customers’ data to hackers, it has resulted in a fall of many companies. Companies have risk falling into endless lawless and may declare bankruptcy when customers’ data are stolen by hackers. Data recovery takes time and can be very expensive. 2 Due to reputational damage to the company, customers will lose trust in it and hence venture to other companies. Therefore resulting in a loss of profits and sales.
In March 2018, data tied to Under Armour’s fitness application was breached and affected 150 million users. Information such as user names, email addresses, passwords was stolen but users’ credit card data and social security or driver’s license numbers were not breached. During after-hours trading, Under Armour’s stock dropped more than 2%. 3
Ways employees’ actions make companies vulnerable to cyber attacks
- Outdated software
The software requires ongoing updates and upgrades. Software becomes outdated when it does not have updates to support it.4 According to PC Trends report 2019,5 1 in 6 Windows 7 users and 1 in 10 Windows 10 users are using an outdated operating system version. Outdated software does not have patches if vulnerabilities are found, resulting in more advanced cyber-attacks. Therefore, it is important to update the software as not updating it expose the business to vulnerabilities and security risks.

- Weak login credentials
Employees having weak or the same passwords across multiple accounts can allow cyber-attacks to take place easily. Principle researcher, Jarno Niemela at F-secure 5 stated that the Brute force attack is the primary way hackers use to bypass the security. It is accounted that 31% of cyber-attacks used this method to hack into their target. Brute force attack means inputting as many passwords possible, seeing if it works against their target. Hackers even have automated scripts that can find a way around simple protection, such as the maximum number of tries of passwords within a certain time window. 6 Hence a simple and common password can easily fall prey to the next cyber-attack.

- Opening unknown emails
In today’s world, emails are the most preferred way of communications when it comes to business-related context. Companies normally collect and stores a huge amount of personal data.7 In order for all of these personal data to be well taken care of, employee’s knowledge and care can play an enormous part in preventing a cyber-attack from happening. A research done by ‘The Radicati Group’8 shows that an average person needs to go through 235 emails a day. With these large amounts of emails, it is not surprising that some may contain scams in the form of attachments or links. With an accidental click, employees may be opening the gates to those cybercriminals into the company’s digital home.
Products available to reduce cyber attacks

Endpoint protection with EDR
EDR means endpoint detection and responses. Its solutions are designed to monitor and respond to advanced internet threats continuously.
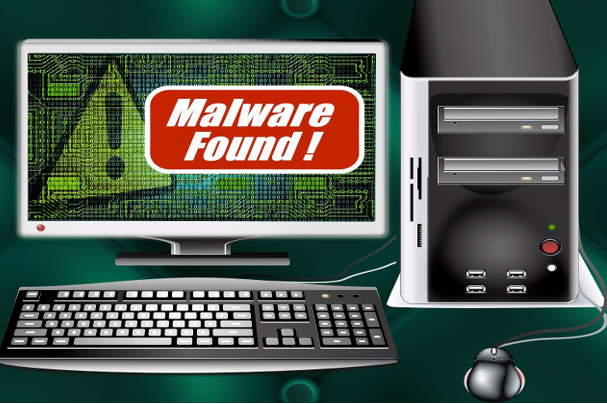
- Remove malware
Endpoint protection provides simple security for business. It automatically removes malware when detected or isolates comprised devices in order to prevent damage. Below are some ways of how endpoint protection removes malware. 9
-
- Isolate devices
In order to prevent the problem from spreading further, part of rectifying a problem is to put it in quarantine. Comprised devices will be isolated when necessary until companies ensure they are safe.
-
- Threat removal
As employees may not be aware of malicious links, attachments or downloads, cyber-attacks may occur once employees click onto those. Therefore with endpoint protection, it will help to remove if anything malicious is found. It is simple and automatic.
-
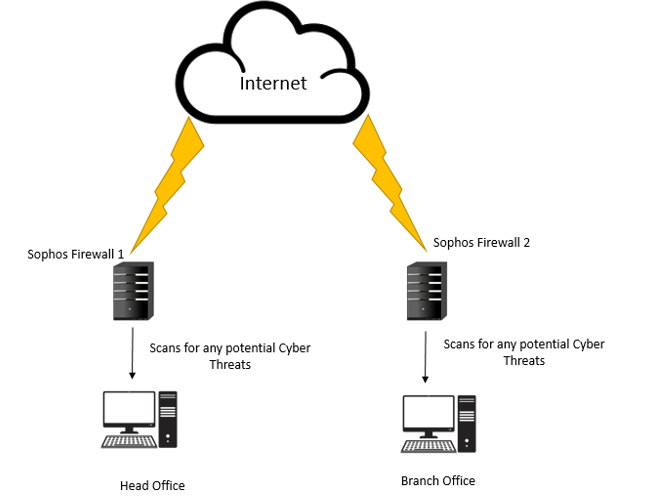
- Synchronised security
Synchronised security transforms threat detection when threat discovery, investigation and response are automated. The incident response time is reduced exponentially and tactical resources can be refocused on strategic analysis.
- Decloaking malware
-
- Behavioural analytics
It helps to find out any suspicious behaviours and allow the detection of malware that is specifically designed to avoid traditional solutions.
-
- Traffic detection
It helps to pre-filter all Hypertext Transfer Protocol (HTTP) traffic and tracks suspicious traffic. Additionally, the file path of the process for the sending of malicious traffic.
-
- Integrated endpoint and network
Suspected system of what exactly firewall is detecting is alerted when there is immediate and automatic communication between Endpoint and Network. It allows the endpoint protection agent to instantly use the information to find out the process behind the attack.
Endpoint backup
Endpoint backup ensures regulatory compliance and improves data visibility for a mobile workforce. It allows employees to protect the corporate data at their convenience. It helps to protect and manage the data across all endpoints such as laptops and smartphones. The unified visibility and search across the data deliver fast identification for governance. To ensure zero-impact to the productivity of end-users, lightweight with tunable resource controls are used. 10
Summary
|
Technology |
Benefits |
|
Endpoint protection with EDR |
· Removes malware o Isolate o Threat removal o Synchronised security
· Decloaking malware o Behavioural analytics o Traffic detection o Integrated endpoint and network |
|
Endpoint backup |
· Ensures regulatory compliance · Improves data visibility · Protects cooperate data at convenience · Fast identification · Zero impact to productivity |
Conclusion
Your company can be a victim of cyber-attack just because of a small mistake made by your employees. Prevent your company from having reputational damage and facing financial losses due to cyber-attacks. Act fast before it is too late!
Click here to find out more about ways or products available to protect your data, or email us to arrange for an appointment with our experienced manager. We will provide ways for you to become more secure.
Author: Toh E Pyn
References
- Services, P. (2019). What Is Cybersecurity?. [online] Cisco. Available at: https://www.cisco.com/c/en_sg/products/security/what-is-cybersecurity.html [Accessed 11 Dec. 2019].
- com. (2019). How cyber attacks impacts business.. [online] Available at: http://www.webrtcworld.com/topics/from-the-experts/articles/440430-how-cyber-attacks-impacts-business.htm [Accessed 11 Dec. 2019].
- Anon, (2018). Under Armour announces data breach, affecting 150 million MyFitnessPal app accounts. [online] Available at: https://www.washingtonpost.com/news/the-switch/wp/2018/03/29/under-armour-announces-data-breach-affecting-150-million-myfitnesspal-app-accounts/ [Accessed 11 Dec. 2019].
- Parker Software. (2019). The security risks of outdated software – Parker Software. [online] Available at: https://www.parkersoftware.com/blog/the-security-risks-of-outdated-software/ [Accessed 11 Dec. 2019].
- Windows Report | Error-free Tech Life. (2019). 55% of Windows PCs are running outdated software [Security Alert]. [online] Available at: https://windowsreport.com/outdated-software-security-risks/ [Accessed 11 Dec. 2019].
- Palmer, D. (2019). Ransomware attacks: Weak passwords are now your biggest risk | ZDNet. [online] ZDNet. Available at: https://www.zdnet.com/article/ransomware-attacks-weak-passwords-are-now-your-biggest-risk/ [Accessed 11 Dec. 2019].
- com. (2019). Weak and Stolen Passwords | WatchGuard Technologies. [online] Available at: https://www.watchguard.com/wgrd-solutions/security-topics/weak-and-stolen-passwords [Accessed 11 Dec. 2019].
- com. (2019). [online] Available at: https://www.kaspersky.com/resource-center/preemptive-safety/7-ways-to-cyberattack-vulnerability [Accessed 11 Dec. 2019].
- com. (2019). [online] Available at: http://www.radicati.com/wp/wp-content/uploads/2015/02/Email-Statistics-Report-2015-2019-Executive-Summary.pdf [Accessed 11 Dec. 2019].
- com. (2019). Sophos Endpoint Protection. Advanced Security with Intercept X.. [online] Available at: https://www.sophos.com/en-us/products/endpoint-antivirus.aspx?cmp=36476&utm_source=GoogleSearch&utm_medium=cpc&utm_campaign=MG-ASEAN-GoogleSearch&utm_content=SM100289&gclid=Cj0KCQiA_rfvBRCPARIsANlV66MbtXXPIGuBJKxEogN28oUqQ4DVaWc9RDWV4eCoEqvCVa3-wTPZn7IaAkVnEALw_wcB [Accessed 11 Dec. 2019].