LIVE Webinar | Understanding SME’s Obligation in Data Protection and Cybersecurity
Zooming into the responsibilities of Business, IT and Compliance during and post COVID-19
26 June 2020 | 2.30 PM to 4.00 PM
We know the importance of PDPA and we wanted to share that knowledge with our clients so take this opportunity to uncover what PDPA means for your company and department through this complimentary webinar with Straits Interactive, one of the experts in the field of data protection.
SMEs today operate in an increasingly connected and competitive digital economy where individuals’ online and real-world activities generate huge amounts of data, especially during circuit-breaker where everyone must work remotely from home.
SMEs have had to scramble to arrange employees to connect back to the office. Have you taken a look at the privacy and IT risks involved in using the free apps as well as the paid apps? Do you know what you need to look out for? No matter how good your multiple cybersecurity tools are, an attacker will eventually find a way into your network through vulnerabilities during a lapse. Join us for the 1-hour session with Straits Interactive to find out about the role and accountability of IT departments, and approach to mitigate the cyber threat and risk.
Topics covered:
- Latest PDPA updates
- Digitalisation & WFH Risks
- Roadmap to PDPA Compliance
- The common problems faced by businesses
- eSentinel™ – 360° Defense in Depth
- and many more!
The Presenters:
- Alvin Toh, Chief Marketing Officer, Straits Interactive Pte Ltd
- Kenneth Wee, Commercial Director, Netpluz Asia Pte Ltd
Webinar: eSentinel™ – 360° Managed Cybersecurity, Simplified
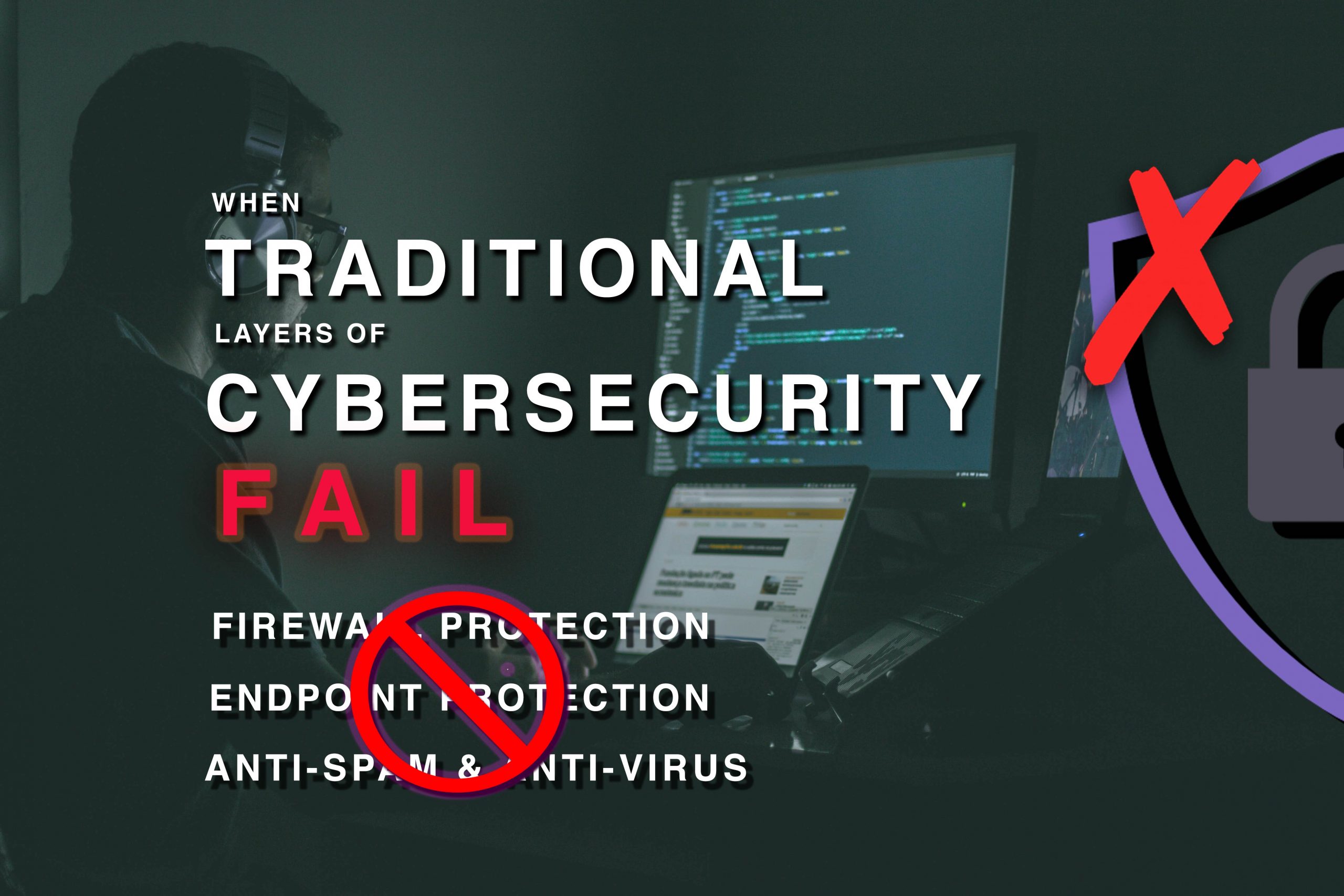
No matter how good your multiple cybersecurity tools are, an attacker will eventually find a way into your network through vulnerabilities.
Once cybercriminals acquire unauthorised access, you can only depend on the speed and performance of your IT team, to identify the threats, to manage multiple platforms to mitigate the attack. However, the time to respond and mitigate could last for hours or even days.
Join us for the 1-hour session to find out how you can now extend your cyber defense perimeter at the ISP level
We will be covering topics such as:
- The Cybersecurity landscape
- The common problems faced by businesses
- What is eSentinel™?
- 360° Defense in Depth
- and many more!
Webinar recording and presentation slides coming soon!
An ounce of prevention through Vulnerability Assessment and Penetration Testing (VAPT) is worth a pound of cure
We all have witnessed the notorious cyber-attacks like WannaCry and NotPetya/ExPetr.1 These high profile attacks have resulted in large disruptions, forcing businesses to halt their operations that may cost them billions of dollars.
According to Accenture, 43% of cyberattacks are targeted towards small businesses. Yet, only 14% are capable of defending against these malicious attacks.2
Obviously, a comprehensive security service will incur additional expenses. However, according to Hiscox, these cyber-attacks can cost your business on average $200,000 regardless of the scale of your business.2
Regardless of the size and scope, your business is greatly vulnerable to cyber-attacks. It is not a matter of if, but it is a matter of when you will be the next target of the hackers’ “hit list”. When it happens, your business may suffer unfathomable consequences.
Stay Free from Cyber Attacks
Now knowing your vulnerability, how can you prevent such malicious cyber activities from occurring? The most ideal and unsurpassable method is through Vulnerability Assessment and Penetration Testing (VAPT). So, you might wonder what this long piece of jargon is about and how and how it is going to protect your business.
This blog article will provide you with some valuable information on:
1. A better comprehension on VAPT
2. How VAPT is executed
3. How VAPT will improve your IT security
What is Vulnerability Assessment & Penetration Testing (VAPT)? 3
To put it in the simplest terms, Vulnerability Assessment and Penetration Testing (VAPT) is a comprehensive and extensive testing process. Its goal is to identify security flaws in your network, application or program.
As the name implies, there are two separate components to perform VAPT. Both Penetration Testing and Vulnerability Assessment execute two completely different types of security tests:
- Vulnerability Assessment: Finds flaws and vulnerability in software, network or program. In other words, to assess how defenceless your systems are.
- Penetration Testing: Conducted after identifying the Vulnerabilities. Security professionals will check and exploit the existing vulnerabilities identified in the software, network or program.
What is Vulnerability Assessment?
By pure definition, the word “Vulnerability” means being exposed to the possibility of getting attacked or harmed. Similarly, a Vulnerability Assessment will provide you with a list of possible security vulnerabilities in your company’s network.
Vulnerabilities can be the result of weak passwords, software errors, wrong software settings, computer virus, or other forms of malicious script or SQL injections.4
Vulnerability Assessment is performed using a non-intrusive approach. With the amalgamation of manual and automated scans, this will enable you to identify security flaws that may be exploited during a cyber-attack.
Here is an example to give you a better grasp on what is a vulnerability and an exploit: If an intruder could bypass the security guard at the front gate by entering the building through a backdoor – this is a vulnerability. If he/she actually get into the building – this is an exploit. It is important to understand the difference between these two words as we will be using it frequently in this blog.
What is Penetration Testing? 3
On the contrary, Penetration Testing employs an intrusive approach. Why would we say it is intrusive? Well, penetration testers would actually attempt to exploit identified vulnerabilities to gain unauthorized access into your IT infrastructure. In a way, it emulates a “real attack” to your IT network.
Upon successfully performing a penetration test, this would allow you to determine how robust your organisation is when it comes to defending your IT network.
The following information will help you understand how these tests are performed for your business.
How are Vulnerability Assessments Performed? 5
As mentioned previously, manual and automated testing tools are utilised to scan your IT infrastructure and environment for known vulnerabilities. During the assessment process, it involves three periodic steps: Assessment, Identifying Exposures and Addressing Exposures. Let’s look at each phase briefly:
1. Assessment
Assessment includes information gathering, defining the parameters and informing the appropriate personnel in your company on the procedure of the assessment.
2. Identify Exposures
This step includes reviewing the results from the previous assessment (the first step) and rectify the vulnerabilities by forming alternative actionable solutions for your network.
3. Address Exposures
At the final step, an investigation is carried out to determine if there are pregnable services in your IT infrastructure. If such vulnerabilities transpire and if the services are not critical to your business, they should be disabled.
Once these security weaknesses are reaffirmed from the investigation, your company will be informed of any lingering and unpatched vulnerabilities. These need to be rectified and patched by your company to mitigate the risk of a cyber-attack.
How are Penetration Tests Performed? 5
Now that you understand how Vulnerability Assessments are performed, the following 5 steps will briefly describe how a Penetration Test is carried out on your IT infrastructure:
1. Planning & Preparation
The very first step will involve developing clear objectives and scope of the penetration test. The details will include the time, duration and potential impact to your business operations during the penetration test.
2. Information Gathering and Analysis
At this step, a list of potential targets will be formed to be evaluated during the vulnerability assessment. These targets identified are established based on the accessible systems within your IT framework.
3. Vulnerability Detection
Similar to a Vulnerability Assessment, to identify vulnerabilities in your network, penetration testers will utilize manual and automated tools.
4. Penetration Attempt
After performing the third step (Vulnerability Detection), penetration testers would identify suitable targets to begin an intrusive attack to test the system’s defences. All these tests are performed at the within a particular time frame that you have agreed upon.
5. Reporting and Cleaning
Last but not least, a report will be summarised and submitted to you. They include: The Penetration Testing Process; Vulnerability Analysis; Commentary of Vulnerabilities Identified.
You could be worried that these exploitation attempts during tests could affect your IT systems. Do not fret.
To ensure that your accustomed business operations are not affected, the final step will require a complete mandatory clean-up of your systems during the penetration test.
We are sure on what we have shared above have overloaded you with information that could be difficult to digest. Not to worry, here is a quick summary about Vulnerability Assessment and Penetration Testing (VAPT):5
|
|
Vulnerability Assessment (VA) |
Penetration Testing (PT) |
|
Purpose: |
Identify exploitable security vulnerabilities in your IT network. |
Perform actual staged attacks and exploit all vulnerabilities in your IT network. |
|
Type of Reports Provided: |
A list of vulnerabilities that will require patches. The vulnerabilities are sequenced based on its criticality. |
A specific and detailed list of information regarding the data compromised and vulnerabilities exploited. |
|
Characteristic: |
List-oriented |
Goal-oriented |
|
Steps to Perform VA/PT: |
3 Steps:
|
5 Steps:
|
Benefits of VAPT6
We do understand if your company were to invest its money and resources in cybersecurity solutions, there need to be a substantial benefit.
If the above information did not convince completely on why you should fund and conduct such IT security tests yet, consider the following three major benefits that VAPT will bring to your business:
1. Extensive application and data security:
Your business will have the confidence that your internal and external systems, software and applications will be meticulously validated for vulnerabilities.
In addition, VAPT assists your business in constructing more secure applications, improving data security and protecting your intellectual property.
2. Improved compliance standards:
You would have heard of PCI-DSS, ISO/IEC 27002 and other security standards that your company have to oblige due to certain regulations. If you are not in compliance with them, expensive fines could be incurred to your company.
To make this process easier for you, VAPT testing identifies if your IT infrastructure is in compliance with the industry standards and government regulations.
3. Security is built into the process during development:
VAPT provides an efficient and practical method to build secure software, application or program. The primary reason for this is that security is part of the development process.
In the event that your IT network gets compromised, it will require expensive fixes and patches after a vulnerability has been exploited by an attacker. – Wasting unnecessary time, money and resources.
4. Simplify your IT network security
While reading through this blog, you must be wondering, understandably so, how you can manage such complicated cybersecurity solutions. You can see how complex it is to perform VAPT itself.
Here is another issue. If you are always being bombarded with various IT security services and needing to purchase them from different vendors, this becomes a continuous hassle and cost. At Netpluz Asia, we simplify this for you with our managed Security Operations Centre (SOC).
As the popular saying goes, “Prevention is better than cure”. Our SOC can deliver industry-leading tools, technology and expertise to secure your valuable digital assets around the clock at a fraction of the cost. If you wish to find out more about our Managed Security Services, please click here.
Summary
Currently, most enterprises are well equipped with sophisticated and highly efficient security apparatus and software. Hackers are constantly looking for new vulnerabilities to hack into your systems. As a result, cybersecurity has become the most crucial component of any company’s infrastructure.
Vulnerability Assessment is one of the first steps in improving your IT security within your business. When it is executed together with Penetration Testing the two combined operations will create a strong deterrent to cyber-attacks that target your company. Identifying security loopholes and possible damages they can pose are important factors you need to pay attention to when protecting your network from malicious attacks.
This is why many companies have been taking care of their digital assets through VAPT testing. It is an obvious fact that IT security services would incur additional costs for your company, but it is less costly than having your network system partially or fully compromised.
If you wish to find out more information on how you can protect and defend your IT business network through Vulnerability Assessment and Penetration Testing (VAPT), you can visit us at Netpluz 24/7. Alternatively, you may book an appointment by submitting your information here for a free consultation.
Author: Shaun Nisal Peiris
Reference
1 Snow, John, et al. “Top 5 Most Notorious Cyberattacks.” Daily English Global Blogkasperskycom, https://www.kaspersky.com/blog/five-most-notorious-cyberattacks/24506/.
2 Scott Steinberg, special to CNBC.com. “Cyberattacks Now Cost Companies $200,000 on Average, Putting Many out of Business.” CNBC, CNBC, 13 Nov. 2019, https://www.cnbc.com/2019/10/13/cyberattacks-cost-small-companies-200k-putting-many-out-of-business.html.
3 “Vulnerability Assessment and Penetration Testing.” Veracode, 22 Oct. 2019, https://www.veracode.com/security/vulnerability-assessment-and-penetration-testing.
4 Infosec, Cyberops. “What Is VAPT and Why Would Your Organization Need VAPT?” Medium, Medium, 15 May 2019, https://medium.com/@cyberops/what-is-vapt-and-why-would-your-organization-need-vapt-444a684c8933.
5 “Vulnerability Assessment and Penetration Testing.” Cyber Security Agency, https://www.csa.gov.sg/gosafeonline/go-safe-for-business/smes/vulnerability-assessment-and-penetration-testing.
6 Prole, Ken. “Vulnerability Assessment and Penetration Testing (VAPT).” Code Dx, 15 Feb. 2019, https://codedx.com/blog/the-perfect-union-vulnerability-assessment-and-penetration-testing-vapt/.
What happened recently with so much Data Breaches news coverage?
One of the key challenges for organisations today is how to safeguard their information systems and digital infrastructure from attacks by malicious hackers and cybercriminals. Current concerns for most companies are often related to data breaches, with so much media coverage focusing on recent cases.
In light of recent data breaches discovered on Singtel and Ninja Van, Personal Data Protection Commission (PDPC) mentioned:
“Despite having received professional advice to take precautions against such vulnerabilities, the organisation omitted to conduct a full code review…and hence failed to discover (the vulnerability) that was exploited in this case.”
No matter how certain organisations are about their defences, there are always risks to their security because of frequent changes and updates made to their digital infrastructure.
Due to these issues, vulnerability assessment and penetration testing (VAPT) come in place as a solution to identify the unknown vulnerabilities and set immediate remediation to mitigate cybersecurity risk for the company.
According to PDPC, eight organisations were found to be in breach of the Personal Data Protection Act (PDPA).
- Ninja Logistics for failing to put in place reasonable security arrangements to protect customers’ data in relation to a tracking function on the company’s website, allowing the data to be accessed publicly.
- EU Holidays, penalty of $15,000, for not protecting customers’ personal data and not having written policies and practices to comply with the PDPA.
- Marshall Cavendish ($40,000), Singtel ($25,000) and SearchAsia Consulting ($7,000); and a warning issued to another two – Tan Tock Seng Hospital and CampVision.
- Directions were also imposed on iClick Media for breaching the Accountability Obligation.
Is Your company ready for Vulnerability Assessment & Penetration Testing (VAPT)?
Vulnerability Assessment & Penetration Testing (VAPT) is necessary to spot your vulnerability. VAPT result shall deliver quality assessment through the eyes of both a hacker and an experienced and certified security expert to discover where you can improve your security posture.
The findings (vulnerabilities) would be delivered as reports that shall be used to effectively remediate any of the vulnerabilities and answer these following questions:
- How vulnerable are you from the internet or intranet?
- What are the exploitable vulnerabilities?
- Are the operating system patches current?
- Do you have unnecessary service running?
“Knowing your vulnerability and the way in which the attackers could exploit them are one of the greatest insights you can get in improving your security program.”
Want to know how we can help you discover vulnerabilities through VAPT?
Reference
Singtel fined $25,000 and Ninja Van $90,000 for data breaches, The Strait Times, Nov 5, 2019. – https://www.straitstimes.com/business/companies-markets/singtel-fined-25000-and-ninja-van-90000-for-data-breaches
New Commission’s Decisions on 4 November 2019, PDPC, Nov 4, 2019 – https://www.pdpc.gov.sg/pdpc/news/latest-updates/2019/11/new-commissions-decisions-on-4-november-2019